Cleveland Clinic sourcing leader offers wise strategies

The digital connections that transform an organization’s systems and processes also can create supply chain vulnerabilities, and the COVID-19 pandemic has increased those risks for healthcare systems. The Cleveland Clinic defense strategy relies on close partnerships between leaders in sourcing, cybersecurity and the legal departments, says John Dockins, Executive Director of IT and Non-Clinical Sourcing.
Advertisement
Cleveland Clinic is a non-profit academic medical center. Advertising on our site helps support our mission. We do not endorse non-Cleveland Clinic products or services. Policy
A key area of focus, Dockins says, is the potential for vulnerabilities in unexpected places.
“Many organizations remain focused on first party risks typically seen through things like email phishing and data breaches on IT infrastructure,” Dockins says. “However, third party system breaches continue to be on the rise, and supply chain experts must remain diligent in monitoring the entire supply network for cyber risks and fraud. Understanding the entire supply network from raw materials to final delivery is paramount in minimizing negative impacts to business operations.”
Dockins leads sourcing for nonclinical supplies, which includes things like software and hardware, servers, personal computers and smart phones, as well as landscaping, snow removal, office supplies, uniforms and construction. He brings a holistic view to protecting the supply chain because of the interconnectivity in the complex healthcare environment.
For example, while it might be counterintuitive to think of something like a sprinkler system containing a measure of risk, if the system is digitally controlled, it can create a potential risk to the larger hospital network.
Dockins cites the example of a data breach at a retail chain, where hackers accessed sensitive customer information through an unexpected back door — the air conditioning system that was linked to the organization’s computer network. “Hackers find a door,” he says. “Think of it as trying to breach the perimeter of a building that has a chain link fence and barbed wire with security cameras around that perimeter. There’s probably still a weak spot where cameras are not covering and the fence could be breached.”
Advertisement
Data, Dockins says, is the holy grail for cyber criminals bent on breaching systems, and hospitals have sensitive information on patients, employees and donors. They also have many points of connection to the system that holds data, from digital door locks to payroll to the kinds of health records that used to be a matter of paper in file folders. The digital tools that make so many things better and easier also can make things easier for criminals.
“It’s kind of hard for a hacker to get a paper file,” Dockins says. “That requires physical theft. But nowadays, everything is moving to a digital state. More is being moved to the cloud, which is just a fancy term for ‘someone else’s computer in someone else’s building.'”
At Cleveland Clinic, Dockins’ says, strong partnerships across departments create multiple levels of administrative and technical controls. That begins at the purchase point.
“If someone wants to buy something new, there are a lot of checks and balances. We evaluate not only the vendor, but we evaluate the product,” Dockins says. “We must answer the questions of where the parts are coming from. Are they manufactured with the latest security specifications? What data is being collected and how will the data be secured during transmission, processing and storage?”
Vendors are selected after thorough due diligence. For example, if a small-scale or unknown vendor is offering a better price on a piece of equipment, Dockins wants to be sure he understands the reason. “If the equipment is a document scanner, for example, then we have to think about how the scanner is going to be connected to our network and what documents the hospital might scan through it.”
Advertisement
Dockins recommends that organizations build an internal team that closely considers any product that is attached to the network. Procurement team members need to perform due diligence during sourcing. Cybersecurity must be involved to ensure that the most up-to-date systems are in place for protecting the network, and to monitor and mitigate cyber risks. And the legal team’s job includes ensuring that contract language protects the enterprise in case a breach occurs.
In general, he adds, it can be a good strategy to identify trusted vendors and increase business with them whenever possible. “Fewer vendors with the adequate risk posture ultimately can reduce risk.”
Dockins also recommends explaining the logic of security measures to everyone at the enterprise. Most importantly, everyone must understand their role and contribution in managing the complex risk landscape.
“You can find USB ports on most equipment today,” Dockins says. “People need to be aware that just because there is a port available doesn’t mean it’s safe to charge a smart phone on that port. Sometimes good people aren’t thinking about the potential risk of something that seems so mundane.”
Dockins also recommends adding cybersecurity compliance to regular employee training curriculum. “We have to be more diligent about thinking of those cyber threats, because they are real.”
Advertisement
Advertisement

Advanced software streamlines charting, supports deeper patient connections

How holding simulations in clinical settings can improve workflow and identify latent operational threats

Interactive Zen Quest experience helps promote relaxing behaviors

Cleveland Clinic and IBM leaders share insights, concerns, optimism about impacts
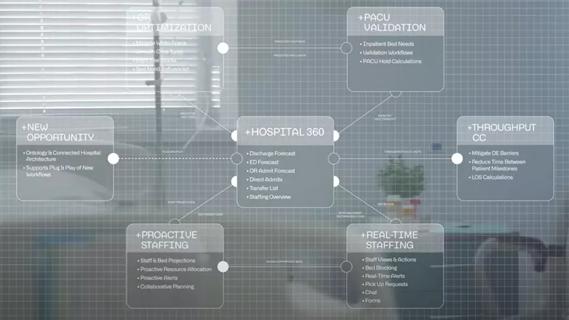
Cleveland Clinic partners with Palantir to create logistical command center

A Q&A with organizational development researcher Gina Thoebes

Cleveland Clinic transformation leader led development of benchmarking tool with NAHQ

Raed Dweik, MD, on change management and the importance of communication